Every security system needs a lock. In the world of blockchain, that lock is built not with steel, but with mathematics. To understand how a decentralized network can be more secure than a bank vault, we must first master the concept of Hashing.
What is a Hash?
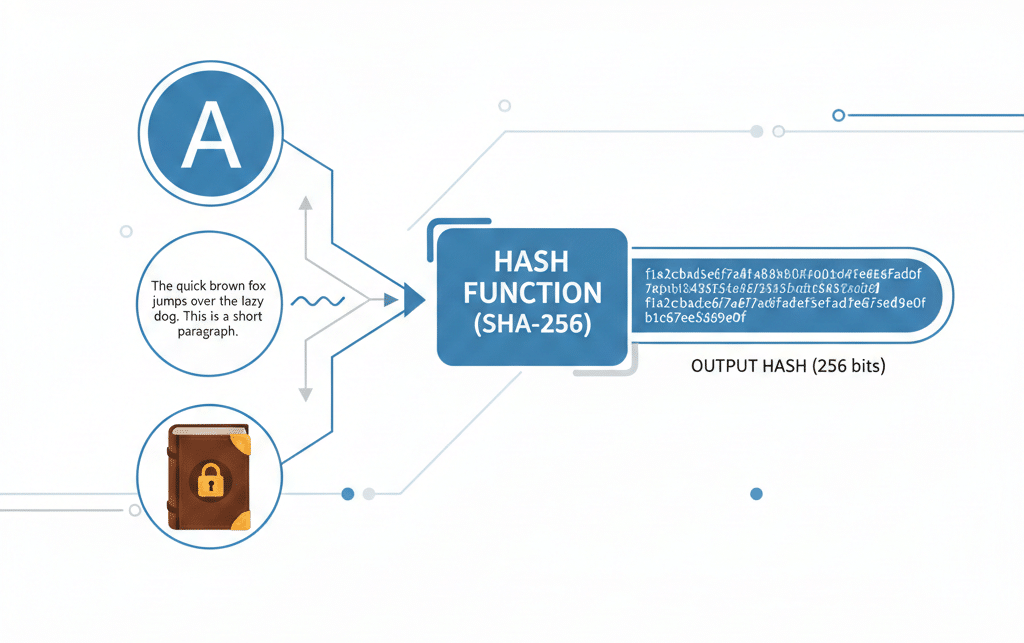
A hash is a unique digital fingerprint created for a piece of data. Whether it is a single word, a long list of transactions, or a massive database, a hashing algorithm will always produce a fixed-length string of letters and numbers.
You can feed any amount of data into a special hashing algorithm, a document, a paragraph, or a long list of transactions. The algorithm will always produce a fixed-length string of letters and numbers. This is the hash.
No matter how many times you put the exact same data into the algorithm, you will get the exact same hash every time. Think of hashing as a highly sophisticated digital blender that takes any input and creates a unique, fixed-size output. This output, the Hash, is the digital fingerprint that confirms the integrity of every block in the chain.
The most important feature of a hash is its sensitivity: a tiny change in the original data leads to a completely unrecognizable hash.
What is the Hash Function?
A Hash Function is a mathematical algorithm that converts any form of data, text, a picture, a whole database into a short, unique alphanumeric string.
In the world of Bitcoin and many other blockchains, the specific algorithm used is called SHA-256 (Secure Hash Algorithm 256 bit).
For our purposes as students of blockchain, we need to understand the four key properties that make this function a perfect digital protector.
Property 1: Deterministic Output (Always the Same)
The first rule of hashing is consistency: If you use the same input, you must get the exact same hash output, every single time.
Imagine putting the word “SECRET” into the SHA-256 blender. It might output a hash like 998C4E…
If you run the word “SECRET” through the function a million times, the result will always be 998C4E…
This predictability is essential for verification. When a node checks a block, it simply runs the block’s data through the hash function and sees if the resulting hash matches the recorded hash.
Property 2: Fixed-Size Output (Always the Same Length)
No matter how large or small your input data is, the output hash will always be the same length. For SHA-256, the output is always 256 bits, which translates to 64 characters of letters and numbers.
You could hash the letter “A” and get a 64-character hash. You could also hash the entire text of the Lord of the Rings trilogy and still get a 64-character hash.
This is important because it makes it impossible to guess the size or complexity of the original data just by looking at the hash.
Property 3: One-Way Function (Irreversible)
Hashing is a one-way street. It is easy to go from the data (input) to the hash (output). However, it is virtually impossible to go backward—to take the hash and figure out the original data.
Think of it like cooking: You can easily mix flour, eggs, and sugar to bake a cake. But you cannot take a baked cake and perfectly separate it back into the raw flour, eggs, and sugar.
This one-way nature protects the privacy of the data. Even though the hash is public, the original transactions remain secure and hidden within the structure.
Property 4: The Avalanche Effect (Total Change)
This is the most critical property for immutability. Even the smallest possible change to the input data creates a massive, unpredictable change in the output hash. This is called the Avalanche Effect.
If you change the sentence “I sent $10.00 to Bob.” to “I sent $10.01 to Bob” (a change of one cent), the resulting $64-character hash will be completely different. Over half the characters in the hash will change randomly.
Why Hashing is the Perfect Digital Fingerprint
These four properties combined are why the hash function is the digital protector of the blockchain:
- Integrity Check: The deterministic nature (Property 1) allows everyone to quickly verify if the data in a block is correct.
- Security Barrier: The one-way nature (Property 3) means a hacker cannot reverse the hash to uncover private information easily.
- Tamper Proofing: The avalanche effect (Property 4) ensures that any attempted change to a block instantly breaks the cryptographic chain, making the fraud immediately visible to the entire distributed network.
Hashing is the mathematical key that allows us to build trust in a trustless environment.
Disclaimer:
Some elements of this content may have been enhanced with the help of our artificial intelligence (AI) assistants for purposes such as basic refinement, review, image generation, and translation to deliver high-quality news in a shorter time frame. However, all AI-assisted content is reviewed and approved by our team to ensure accuracy, fairness, and editorial integrity.