A new research paper last month has sent shockwaves through the cryptocurrency world, posing a question many hoped was decades away: Could a quantum computer steal your Bitcoin in just nine minutes? According to a detailed whitepaper recently released by Google’s Quantum AI team, on March 31, 2026, the math says yes.
But before you panic-sell your digital assets, here is the immediate reality check: No one has hacked Bitcoin with quantum computing today. Current hardware is still too noisy and small-scale to execute this kind of attack.
Co-authored with experts from Stanford University, UC Berkeley, and the Ethereum Foundation, the whitepaper is not a breaking news alert of an active exploit. Instead, it is a highly calculated, forward-looking warning designed to force the crypto industry to upgrade before a real threat emerges.
The Anatomy of a 9-Minute Hack
To understand the threat, we have to look at how Bitcoin secures your money. The network relies on Elliptic Curve Digital Signature Algorithm (ECDSA) cryptography. In simple terms, your wallet has a public key (like a bank account number) and a private key (your secret PIN).
When you send a transaction, your public key is briefly exposed to the network so miners can verify it. A sufficiently powerful quantum computer running Shor’s algorithm can reverse-engineer your private key from that exposed public key much faster than a classical computer.
Because Bitcoin’s average block confirmation time is about 10 minutes, the window for this “on-spend” attack is incredibly tight. However, Google’s researchers found that an attacker could pre-compute half the work in advance, letting the machine sit in a “primed” state.
Once your transaction hits the mempool and the public key is visible, the primed quantum machine can finish cracking the key in just 9 to 12 minutes. With a single machine, an attacker would have roughly a 41% chance of deriving your private key and stealing the funds before the original transaction confirms.
The Hard Numbers: A Shrinking Qubit Threat
For years, experts believed a quantum hack would require tens of millions of physical qubits. This was a milestone considered to be decades away. Google’s new estimates completely shatter that timeline.
By heavily optimizing Shor’s algorithm circuits, researchers found they only need about 1,200 logical (error-corrected) qubits. On realistic future hardware, this translates to fewer than 500,000 physical qubits in total.
This represents a staggering 20x reduction in the computing resources previously thought necessary. While a Cryptographically Relevant Quantum Computer (CRQC) does not exist yet, Google’s announcement that they are targeting a full internal migration to Post-Quantum Cryptography (PQC) by 2029 suggests the engineering gap is closing faster than anticipated.
Dormant Danger: Billions at Risk
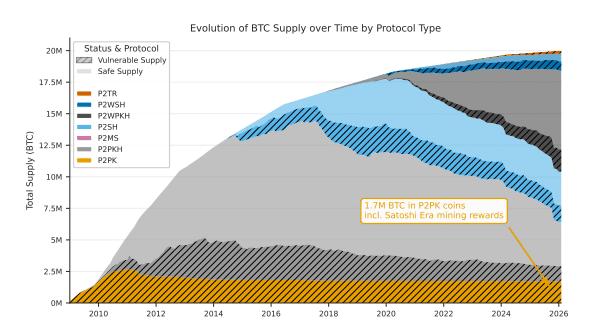
While active transactions face the 9-minute window, billions of dollars in dormant Bitcoin face a much simpler “at-rest” attack. Because these public keys are already permanently exposed on the blockchain, a quantum computer has unlimited time to crack them.
The paper estimates that roughly 1.7 million BTC sit in fully exposed P2PK (Pay-to-Public-Key) scripts from Bitcoin’s early days. The whitepaper further notes that the total amount of dormant quantum-vulnerable bitcoin may reach 2.3 million BTC when all script types are considered — a figure that includes the P2PK holdings, not in addition to them. However, when factoring in all vulnerable protocols — including modern P2TR scripts, reused P2PKH and P2WPKH addresses, and other exposed keys — the following chart puts the total at approximately 6.9 million BTC, or roughly 32% of the circulating supply.
There is, however, a silver lining: Bitcoin’s core Proof-of-Work mining process remains secure. The researchers noted that Grover’s algorithm—a different quantum computing technique—does not give attackers a practical edge against the network’s massive hash rate because it only provides a quadratic speedup, which can be mitigated by simply increasing the network’s difficulty.
Vitalik Buterin and the “Q-Day” Reality Check
The looming threat of a quantum breakthrough is widely referred to in the crypto space as “Q-Day“—the theoretical date when quantum machines officially break our current cryptographic standards. High-profile industry leaders are no longer ignoring it.
Ethereum Co-Founder Vitalik Buterin has been highly vocal about Q-Day. He recently estimated there is roughly a 20% chance that quantum machines capable of breaking modern encryption could arrive before 2030, with a risk window opening as early as 2028.
To prepare for a potential “quantum emergency,” Buterin has already proposed an Ethereum defense strategy. His roadmap involves transitioning to quantum-resistant, hash-based signatures and preparing a “simple recovery fork” that could be deployed to freeze and protect user funds if a sudden quantum leap occurs.
Industry Response: The Push to Upgrade
Major tech players are already preparing for this quantum shift. Google has set an aggressive internal target of 2029 to migrate all its systems to post-quantum cryptography (PQC), urging the broader tech community to follow suit.
The crypto industry is beginning to echo this urgency. Following the paper’s release, Coinbase CEO Brian Armstrong publicly addressed the looming threat: “Going to start spending time on this personally—seems like we all need to solve it sooner rather than later.”
Central to this mission is accelerating the adoption of “BIP-360,” a proposal to introduce Winternitz One-Time Signatures (WOTS+) to the Bitcoin network. These “hash-based” signatures are mathematically immune to Shor’s algorithm.
For everyday users, there are practical steps to take right now. The most crucial rule: Stop reusing wallet addresses. By using a fresh address for every transaction and keeping large holdings in cold storage, you ensure your public key remains hidden until the very moment you spend, forcing any attacker into that difficult 9-minute window.
Bottom Line: Evolution, Not Extinction
Transitioning Bitcoin to quantum-resistant signatures will likely require a network-wide soft fork. While complex, the Bitcoin community has successfully executed massive upgrades before, such as SegWit and Taproot.
Google’s paper is a technical wake-up call backed by rigorous math and zero-knowledge proofs. The quantum era is coming, and Bitcoin does not have to fear it—it just needs to evolve ahead of it.
Also Read: “Quantum Security Shouldn’t Be a Debate”: Justin Sun Targets Bitcoin & Ethereum
Disclaimer:
Some elements of this content may have been enhanced with the help of our artificial intelligence (AI) assistants for purposes such as basic refinement, review, image generation, and translation to deliver high-quality news in a shorter time frame. However, all AI-assisted content is reviewed and approved by our team to ensure accuracy, fairness, and editorial integrity.