In the ancient tale of Icarus, hubris took the form of wax wings soaring too close to the sun. In modern finance, decentralized finance (DeFi) specifically, it manifests as elegant lines of code promising trustless, borderless value—built atop assumptions so thin they can shatter with one forged message.
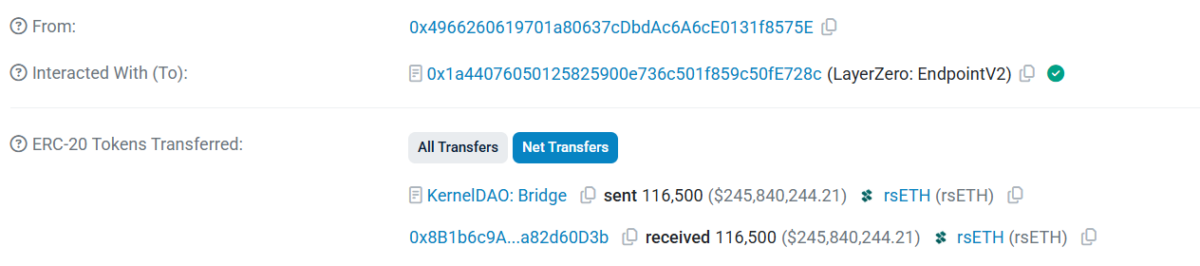
On April 18, 2026, at 17:35 UTC, that philosophical fragility became painfully concrete. A single transaction, originating from a wallet quietly funded through Tornado Cash, exploited KelpDAO’s LayerZero-powered bridge and drained 116,500 rsETH—approximately $292 million at prevailing prices, nearly 18% of the token’s entire circulating supply.
It was not a dramatic zero-day breach of core contracts, nor a sophisticated smart contract reentrancy. It was simpler, and therefore more unsettling, a spoofed cross-chain message that the system accepted as truth.
What followed revealed the deeper tension at DeFi’s heart—the dream of perfect composability colliding with the stubborn reality of human (and machine) fallibility. Unbacked tokens flooded lending pools, bad debt cascaded, and over $13 billion in total value locked evaporated from the ecosystem in under 48 hours.
This led to a rising confidence in DeFi—that invisible glue holding “money Legos” together—being cracked once again.
Not merely a hack, this sophisticated exploit was a stark reminder that in our pursuit of decentralized perfection, we often paper over single points of failure with optimism, defaults, and the quiet hope that “it won’t happen to us.”
The KelpDAO incident forces a deeper question: Can a system truly be trustless when its security rests on configurations that prioritize speed over resilience, or when one compromised verifier can undermine the economic reality of millions?
How One Forged Message Broke the Bridge
KelpDAO had built rsETH as a liquid restaking token, allowing users to stake Ether, earn yield, and still move that value fluidly across Ethereum mainnet and Layer-2 networks. The bridge, powered by LayerZero’s infrastructure, was meant to be the seamless conduit.
The attacker needed no direct access to Kelp’s core restaking logic. Instead, they called the lzReceive function on LayerZero’s EndpointV2 contract, delivering a carefully crafted packet. KelpDAO’s bridge, relying on its verification layer, released the reserves without a corresponding burn on the originating side. This led to unbacked rsETH effectively materialized from nothing.
The critical weakness was KelpDAO’s use of a 1/1 DVN (Decentralized Verifier Network) setup—a single verifier tasked with validating cross-chain messages.
Reports indicate the attackers poisoned RPC nodes feeding this verifier and deployed a DDoS attack to force failover to the compromised path. Once the malicious verifier signed the fake message, the bridge complied.
KelpDAO activated emergency pauses roughly 46 minutes later, thwarting follow-up attempts that could have drained an additional $80–100 million. The swift response limited immediate escalation, but the initial loss struck a protocol holding around $1.57 billion in TVL.
Blame Game: Defaults, Warnings, and Hardening Promises
KelpDAO’s initial statement, posted around 20:10 UTC, struck a cautious tone: “Earlier today we identified suspicious cross-chain activity involving rsETH. We have paused rsETH contracts across mainnet and several L2s while we investigate.”
By April 20, the blame-exchange grew sharper as LayerZero framed the incident as “isolated entirely to KelpDAO’s rsETH configuration as a direct consequence of their single-DVN setup.” They argued that a multi-DVN model—demanding consensus across independent verifiers—would have neutralized the attack despite node compromise.
The team highlighted prior recommendations for stronger setups and declared they would stop signing messages for any protocols still running 1/1 configurations.
KelpDAO countered that the 1/1 setup followed LayerZero’s own documented defaults from their early 2024 integration and had been confirmed suitable during L2 expansions. “Establishing a shared and accurate account of what happened is the foundation for making the right fixes together,” they emphasized. Meanwhile, a joint post-mortem remains forthcoming.
Post-incident reviews showed that nearly half of LayerZero-integrated protocols operated under similar minimal configurations, underscoring how convenience had quietly become widespread risk.
Contagion Spreads: Bad Debt, Freezes, and a $13 Billion TVL Flight
The stolen rsETH found quick utility. Attackers deployed the unbacked tokens as collateral, primarily on Aave V3 and V4, borrowing substantial WETH and other assets. When the collateral’s true backing collapsed, bad debt estimates ranged from $177 million to over $236 million.
Aave acted decisively, freezing rsETH markets on V3 and V4 and reducing loan-to-value ratios to zero. “Aave’s contracts have not been exploited and this is an exploit related to rsETH,” the protocol stated.
Founder Stani Kulechov and teams confirmed neutralized borrowing power against the asset. Further analysis outlined loss scenarios, with commitments to explore offsets via the safety module or other mechanisms. Some WETH reserves on Ethereum Core V3 were later unfrozen for supplying (LTV still at 0), while others stayed paused.
SparkLend, Fluid, and additional platforms mirrored the containment measures. The market response was visceral: Aave experienced outflows estimated to $9 billion in 48 hours while broader DeFi TVL dropped more than $13 billion, with sharp declines rippling across yield and lending protocols.
Read: Aave Faces Mounting Bad Debt Crisis After $292M KelpDAO Exploit
Arbitrum Steps In: The Rare Emergency Freeze
On April 21, Arbitrum’s Security Council invoked emergency powers. They froze 30,766 ETH — roughly $71 million—in an attacker-linked address on Arbitrum One, transferring the funds to an intermediary wallet accessible only through governance.
“The Security Council acted with input from law enforcement as to the exploiter’s identity and, at all times, weighed its commitment to the security and integrity of the Arbitrum community without impacting any Arbitrum users or applications,” the statement explained.
The move recovered approximately a quarter of the haul on that chain, offering a concrete offset amid ongoing recovery talks.
The intervention, while effective against suspected state-linked funds, revived perennial questions about where decentralization yields to necessity.
Who Did It? Lazarus Group in the Spotlight
Attribution, particularly from LayerZero, has coalesced around North Korea’s Lazarus Group, particularly the TraderTraitor subunit. Indicators include Tornado Cash funding, sophisticated RPC poisoning paired with DDoS tactics, and alignment with the group’s historical playbook.
These tactics align closely with the group’s evolving playbook, which has shifted from simple phishing and malware campaigns to precise infrastructure-level attacks on cross-chain messaging systems.
While definitive forensic closure awaits, the signals have strengthened as the leading explanation among investigators and protocol teams. The hack followed a $285 million incident at Drift Protocol earlier in April, pushing monthly DeFi losses past $600 million.
This incident follows closely on the heels of the $285 million Drift Protocol exploit on April 1, 2026, which Chainalysis and others also linked to North Korean actors (tracked under clusters like UNC4736). In that case, a months-long social engineering operation compromised admin access rather than infrastructure, yet both attacks demonstrate the group’s adaptability and persistence.
Together, the two breaches have pushed April 2026 DeFi losses well past $600 million in under three weeks, marking one of the most aggressive state-sponsored campaigns against decentralized finance in recent memory.
Broader and Unrealized Risk on DeFi
A post-incident Dune Analytics review revealed the scale of the problem. Among roughly 2,665 active LayerZero OApp contracts analyzed over the prior 90 days, approximately 47% still operated with the minimal 1-of-1 DVN configuration—the exact security floor that enabled the exploit. Another 45% used 2-of-2 setups, while only about 5% employed stronger 3-of-3 or higher redundancy.
This widespread adoption of low-security defaults stems from the appeal of modular security in LayerZero’s design: developers can prioritize lower latency, reduced gas costs, and faster onboarding over enforced minimum redundancy.
Yet the KelpDAO case demonstrates how such flexibility, when left to individual protocol choices, normalizes single points of failure across the ecosystem rather than mitigating them.
According to Dune, even shifting to multi-DVN configurations may offer limited protection if verifiers share common infrastructure dependencies, particularly the small pool of RPC providers (often clustered on centralized cloud services).
If multiple DVNs rely on overlapping nodes, a sophisticated attacker could still compromise or overwhelm the shared foundation, undermining the redundancy illusion.
Recovery Roads and Lingering Questions
KelpDAO confronts difficult decisions on loss socialization, potential pro-rata haircuts (around 18%), recovery funds, and legal coordination. While no finalized plan has emerged, the focus largely remains on supporting affected holders while containing broader fallout.
This episode exposes DeFi’s central paradox: a movement born from distrust of centralized gatekeepers now grapples with its own emergent points of centralized risk—whether in bridge verifiers, default configurations, or emergency governance powers.
In DeFi, cross-chain bridges remain high-value targets. All the non-custodial collateral in lending markets carries upstream dependencies that risk models struggle to price dynamically. In addition, minimal security choices—often justified by lower latency or simpler onboarding—can metastasize into systemic threats.
LayerZero has pledged accelerated pushes toward multi-DVN redundancy and infrastructure hardening. Yet the incident leaves lingering unease about enforcement, the weight of “defaults,” and whether DeFi’s interlocking components have outgrown our ability to contain isolated failures.
Final words
While the current scenario remains complicated, a detailed post-mortem may clarify responsibility and drive concrete upgrades. This $292 million heist did more than drain reserves—it drained another layer of illusion that DeFi had transcended the old tensions between freedom and security, innovation and prudence.
As of April 21, 2026, the situation evolves with stolen funds continuing to move or being laundered in some vectors; freezes hold in others. Latest report from CertiK revealed that the hacker is moving stolen funds into Bitcoin via THORChain—making the recovery attempt even harder.
Meanwhile Aave continues assessing bad debt sitting in rsETH, while roughly $10 billion leaving the protocol TVL since the exploit.
This reporting is based on official statements, on-chain data, and public updates available through April 21, 2026. The story remains fluid as investigations, governance actions, and recovery efforts progress.
Also read: Crypto’s $606M April Nightmare: 12 Hacks, 18 Days, Worst Month Since Bybit Heist