In the world of cryptocurrency, there is a saying that is both empowering and sobering: “Be your own bank.” This principle of self-sovereignty is the bedrock of Web3, offering unprecedented financial freedom. However, this freedom comes with a critical responsibility: you are also your own security guard.
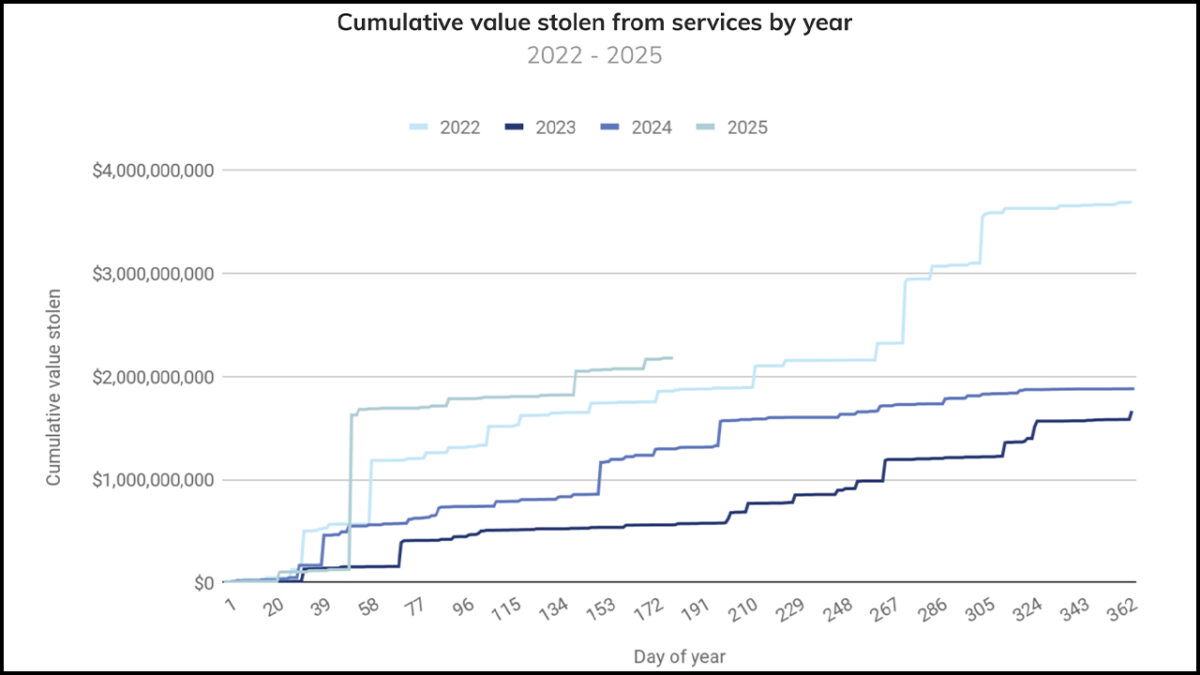
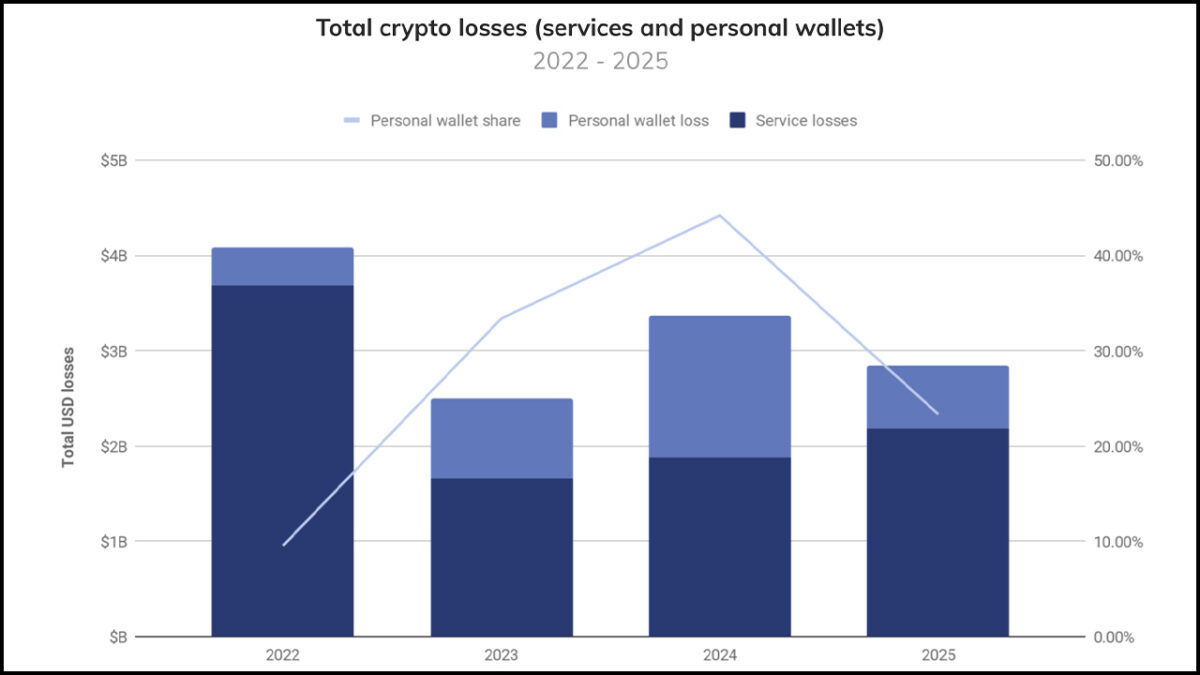
The need for robust security has never been more critical. According to the authoritative 2025 Mid-Year Crypto Crime Update from Chainalysis, over $2.17 billion in digital assets were stolen in the first half of 2025 alone, marking a devastating period for hacks compared to 2024. This staggering figure, driven by events like the historic $1.5 billion hack of the ByBit exchange attributed to the DPRK, highlights a harsh reality: as the value within the crypto ecosystem grows, so do the sophistication and frequency of attacks.
This guide is designed to arm you with the knowledge to protect yourself from becoming another statistic. We will cover everything from the essential security hygiene every user must practice to the advanced techniques required to navigate the world of decentralized finance (DeFi) safely.
The Foundations: Essential Security for Everyone
Before you even think about complex DeFi protocols, you must master the fundamentals. These are the non-negotiable first lines of defense that protect you from the most common attacks.
Password Management
In a world of interconnected services, using the same weak password across multiple platforms is the digital equivalent of leaving your front door wide open. A data breach on one website could give an attacker the keys to your entire digital life, including your crypto exchange accounts.
- Best Practice: Use a unique, strong password (a long combination of upper/lowercase letters, numbers, and symbols) for every single online account.
- The Solution: It’s impossible to remember dozens of complex passwords. Use a reputable password manager. These tools generate and securely store unique passwords for all your accounts, requiring you to only remember one master password.
Two-Factor Authentication (2FA)
Two-Factor Authentication adds a critical second layer of security. Even if an attacker steals your password, they won’t be able to access your account without a second verification code. However, not all 2FA methods are created equal.

Here are the three main types, ranked from least to most secure:
- SMS 2FA (Least Secure): This method sends a code to your phone via text message.
- Risk: It is vulnerable to SIM-swap attacks, where an attacker tricks your mobile carrier into transferring your phone number to a new SIM card they control, allowing them to intercept your 2FA codes.
- Authenticator App 2FA (Good Security): This method uses an app like Google Authenticator or Authy to generate a time-sensitive code on your device.
- Benefit: It is not vulnerable to SIM-swaps and is the standard for good security.
- Hardware Key 2FA (The Gold Standard): This method uses a physical device, like a YubiKey, that you must plug into your computer or tap on your phone to approve a login.
- Benefit: It is the most secure form of 2FA, as an attacker would need to physically steal your hardware key to compromise your account.
Phishing and Scam Awareness
While major exchange hacks capture headlines, attacks targeting individual users are a rapidly growing threat. The Chainalysis report found that personal wallet compromises now account for 23.35% of all stolen fund activity YTD in 2025. Attackers are increasingly focusing on social engineering and phishing scams to trick users into handing over their assets.
Be vigilant for these common tactics:
- Fake Emails & DMs: Attackers impersonate exchanges, projects, or influencers, sending urgent messages that require you to click a malicious link.
- Malicious Links: Never click on suspicious links or download unknown files. These can contain malware designed to steal your data.
- Signature Spoofing: A recent popular tactic involves a malicious dApp tricking a user into signing what appears to be a simple login message, but is actually a transaction that grants the attacker sweeping permissions to drain their wallet. Always read what your wallet is asking you to sign.
Choosing Your Fortress – Understanding Crypto Wallets
The core of self-custody is understanding the difference between your public key (your address, which is safe to share) and your private key (your master password, which must never be shared). The mantra to live by is: “Not your keys, not your crypto.”

Custodial Wallets (The Exchange)
When you keep your cryptocurrency on a centralized exchange like Coinbase or Binance, you are using a custodial wallet. The exchange holds your private keys on your behalf.
- Pros: Easy to use, familiar password-reset functionality.
- Cons: You do not have true ownership of your assets. The exchange is a prime target for hackers and can freeze your funds. The $1.5 billion ByBit hack in 2025 and the Coinbase data breach in May 2025 are critical reminders of the catastrophic risks of centralization, from external nation-state attacks to internal security lapses.
Hot Wallets (Software Wallets)
Hot wallets, like MetaMask or Trust Wallet, are software programs that run on your computer or phone. With a hot wallet, you control your own private keys.
- Pros: You have full self-custody of your assets. They are easy to use for interacting with DeFi applications (dApps).
- Cons: Because they are connected to the internet, they are inherently more vulnerable to malware, viruses, and phishing attacks that could compromise your keys.
Cold Wallets (Hardware Wallets)
Cold wallets, like those from Ledger or Trezor, are physical devices that store your private keys offline.
- Pros: This is the ultimate security standard. Your private keys never touch the internet, making them immune to online hacking attempts. Transactions are signed on the device itself.
- Cons: They cost money to purchase and are slightly less convenient for making frequent transactions.
Recommendation: For any amount of cryptocurrency you are not willing to lose, a hardware wallet is not a luxury; it is a necessity.
The Master Key – Protecting Your Seed Phrase
When you create a self-custody wallet (hot or cold), you will be given a seed phrase (also called a recovery phrase). This is a list of 12 or 24 words that acts as the master backup for your entire wallet. Anyone who has this phrase can access all of your funds.
Protecting it is the most important job you have as a crypto owner.
The Golden Rule: NEVER store your seed phrase digitally
This means:
- NO screenshots
- NO text files on your computer
- NO saving it in a password manager
- NO storing it in cloud services like Google Drive or Dropbox
- NO sending it to yourself in an email
- NEVER type it into any website or give it to anyone claiming to be “support”
Any digital storage of your seed phrase makes it vulnerable to being stolen by malware or hackers.
Best Practices for Storage:
- Write It Down: Use a pen and paper. Write the words clearly and number them correctly.
- Store It Securely: Store the paper in a safe, secure, and private physical location (like a safe deposit box or a fireproof safe at home).
- Create Multiple Backups: Store copies in different, secure physical locations to protect against loss from fire or theft.
- Consider Metal Storage: For ultimate durability, advanced users can engrave their seed phrase onto a steel plate, making it resistant to fire, water, and physical degradation.
Advanced DeFi Security – Interacting Safely
The DeFi space, while innovative, remains a primary target for attackers. When you interact with a DeFi application, you are not just sending tokens; you are often signing a smart contract approval, which grants the protocol permission to move tokens out of your wallet on your behalf. This is a necessary function, but it’s also a major attack vector.
Wallet Hygiene: The “Hot” and “Cold” Approach
Never connect your main hardware wallet, where you store the majority of your assets, directly to a new or untested DeFi application.
- Best Practice: Use a two-wallet system
- Your Cold Wallet (The Vault): Your hardware wallet holds your long-term savings. It rarely interacts with dApps.
- Your Hot Wallet (The Spending Wallet): A MetaMask wallet with a small, disposable amount of funds that you use for experimenting with new protocols. If this wallet is compromised, your main savings remain untouched.
Revoke Your Permissions
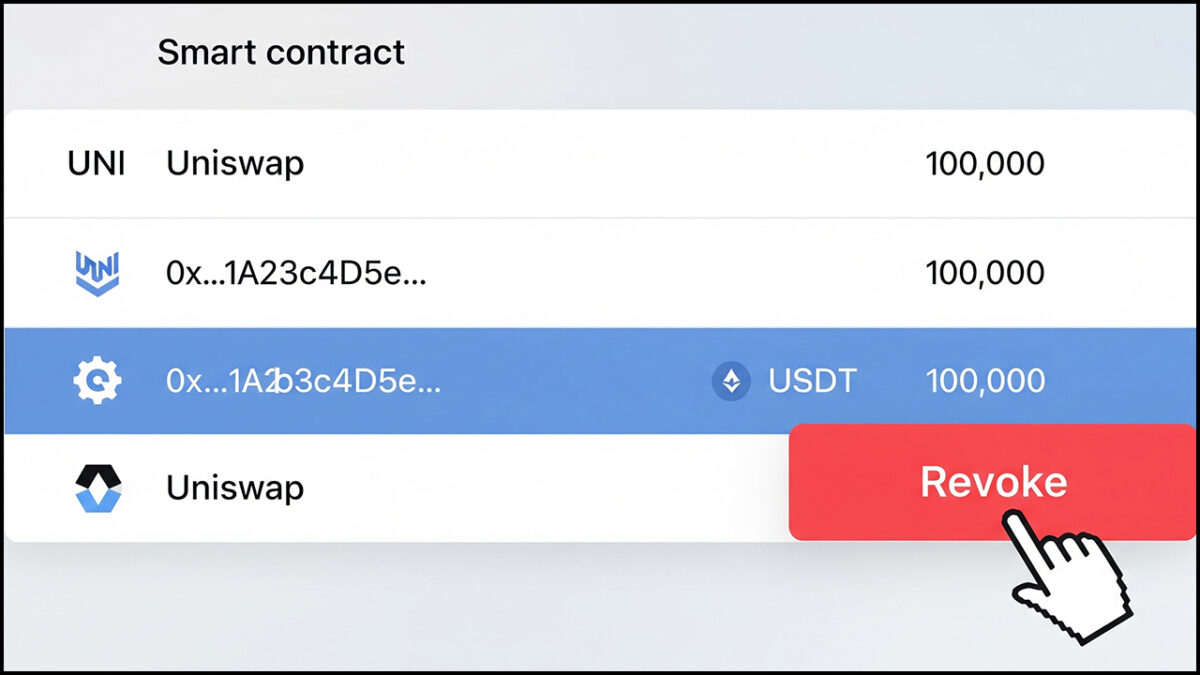
Over time, you will grant dozens of approvals to different dApps. A bug or exploit in an old protocol you haven’t used in months could still be used to drain your wallet if you haven’t revoked the permission.
- Best Practice: Periodically review and clean up your active token approvals.
- The Solution: Use a trusted revocation tool like Revoke.cash. Connect your wallet to see a list of all the permissions you have granted and selectively revoke any that are old, unnecessary, or for protocols you no longer trust.
Conclusion: You Are in Control
The world of digital assets can seem intimidating, with headlines of hacks and exploits dominating the news. However, the vast majority of losses are preventable.
By adopting a layered security approach, combining strong foundational habits with the right wallet strategy and a cautious approach to DeFi, you can dramatically reduce your risk profile. Personal responsibility is the cornerstone of the Web3 revolution. By taking these steps, you are not just protecting your assets; you are taking full control of your financial sovereignty. Stay vigilant, stay educated, and stay safe.
Disclaimer: Some elements of this content may have been enhanced with the help of our artificial intelligence (AI) assistants for purposes such as basic refinement, review, image generation, and translation to deliver high-quality news in a shorter time frame. However, all AI-assisted content is reviewed and approved by our team to ensure accuracy, fairness, and editorial integrity.