The largest DeFi exploit of 2026 did not require a zero-day vulnerability, a novel attack vector, or a flaw in smart contract logic. It required one forged cross-chain message—verified by a single validator—to drain $292 million from a bridge that a developer had publicly flagged as dangerously configured fifteen months earlier.
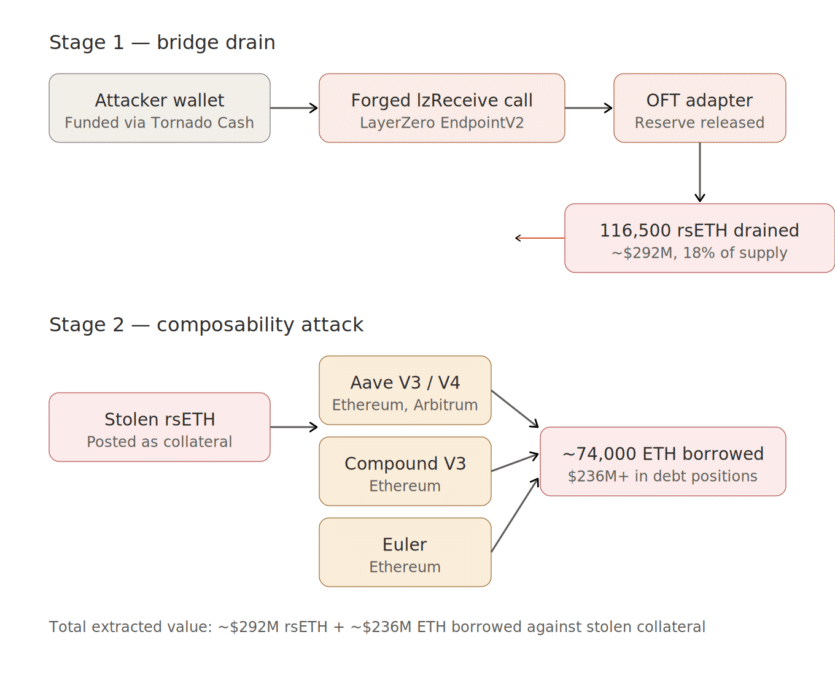
On April 18, an attacker exploited Kelp DAO‘s LayerZero-powered rsETH bridge, stealing 116,500 rsETH. The stolen tokens were immediately deposited into Aave as collateral and used to borrow over $190 million in real WETH.
This led to a chain of bad debt that has since triggered over $10 billion in withdrawals from Aave, emergency freezes across multiple lending protocols, and a $14 billion decline in total DeFi value locked.
The critical context that both LayerZero and Kelp DAO have so far sidestepped in their public statements is that this exact attack surface was flagged—publicly, on the record, in the right forum—over a year before the exploit occurred.
In January 2025, a development team posted on the Aave governance forum warning that Kelp’s 1/1 DVN (Decentralized Verifier Network) configuration created a single point of failure. The post explicitly stated that a single compromised validator signature could trigger the bridge to release funds, and warned that multiple DVN verifications were necessary to prevent such a forgery.
That fifteen-month gap—between a specific, public, technically accurate warning and the exact exploit that warning described—is the detail that makes this incident different from a routine bridge hack.
This was not a case of unknown unknowns. It was a known vulnerability, documented in a governance forum used by Aave’s risk assessors, that was left unaddressed while Kelp expanded rsETH across more than 20 blockchains.
How the Attack Worked
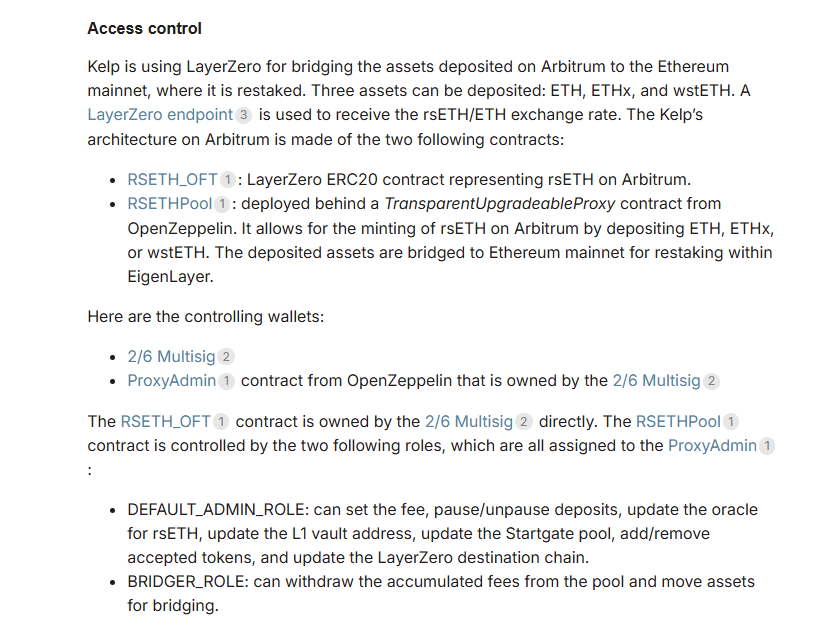
According to LayerZero’s incident statement, the attackers gained access to the list of RPC (Remote Procedure Call) nodes used by LayerZero Labs’ DVN. They then compromised two of those nodes—which were independent nodes running on separate clusters—and swapped out the software running on them with malicious binaries designed to feed the DVN forged transaction data.
Critically, the malicious nodes were engineered to lie selectively. They reported fabricated data only to the DVN, while continuing to tell the truth to every other system querying those same nodes—including LayerZero’s own monitoring infrastructure. This made the attack invisible to internal observability.
Even that was not enough. LayerZero’s DVN uses both internal and external RPCs for redundancy. To complete the attack, the hackers launched DDoS attacks against the uncompromised external RPCs, forcing the DVN to fail over to the poisoned nodes.
Once a failover occurred, the DVN confirmed a transaction that never took place—and the bridge released 116,500 rsETH.
Under a multi-DVN configuration (such as 2/2 or 2/3), this attack would have failed. A second independent verifier would have caught the discrepancy and rejected the forged message. But Kelp’s bridge was configured with a 1/1 setup—one verifier, no backup, no second check.
Kelp’s emergency pauser multisig froze contracts 46 minutes after the drain. Two follow-up attempts, each carrying another 40,000 rsETH (~$100 million), both reverted because of the pause. Without it, total losses could have approached $490 million.
The Blame Game
In its post-mortem, LayerZero stated that “KelpDAO chose to utilize a 1/1 DVN configuration” despite “best practices around DVN diversification” being “previously communicated.” The company framed the incident as an application-layer failure, not a protocol-level one, and confirmed zero contagion to other LayerZero applications.
Kelp DAO, however, has pushed back, with a memo from team sharing that the 1/1 DVN setup is the configuration documented in LayerZero’s own V2 OApp Quickstart guide and shipped as the default for new OFT deployments.
The memo adds that, through a direct communications channel open since July 2024, LayerZero produced no specific recommendation for Kelp to change the rsETH DVN configuration. The compromised DVN, Kelp argues, was LayerZero’s own infrastructure—not a third-party verifier chosen by Kelp.
Recent reports revealed that approximately 40% of all LayerZero applications currently run 1/1 configurations. A Dune analysis of roughly 2,665 active LayerZero OApp contracts found 47% using 1/1 setups.
LayerZero has since announced it will stop signing messages for any application using a 1/1 DVN configuration, forcing a broad migration to multi-DVN architectures.
The Structural Problem
The January 2025 Aave governance warning was not a lone voice. The vulnerability it described—that a 1/1 DVN creates a single point of failure in which one forged signature can drain an entire bridge—is not a novel insight. It is a known design trade-off in LayerZero’s modular architecture. LayerZero’s own CryptoEconomic DVN Framework, launched with Eigen Labs in October 2024, was built specifically to address it.
But the incentive structure pulled in the opposite direction. Under pressure to expand market share, liquid restaking protocols like Kelp opted for OFT-style rapid multi-chain deployment—which is fast, cheap, and using LayerZero’s defaults—rather than the slower, more expensive path of configuring multi-DVN redundancy or deploying native minting on each chain.
This led to what has been the trend since the past few days.
The Kelp exploit is not an isolated application failure. It is a structural warning about default security standards across omnichain infrastructure.
If nearly half of all LayerZero applications use the same minimal configuration that was just exploited for $292 million, the market is going to start distinguishing much more aggressively between protocols that are merely “cross-chain” and those that are meaningfully hardened.
Also read: A $292 Million Wake-Up Call: Inside KelpDAO Hack That Exposed DeFi’s Fragility











