Kelp DAO, one of the largest liquid restaking protocols in the EigenLayer ecosystem with over $1 billion in TVL before Saturday, has been hit with the biggest DeFi exploit of 2026. At 17:35 UTC on April 18, an attacker walked away with 116,500 rsETH, roughly $292 million and about 18% of the token’s entire circulating supply in a single transaction targeting Kelp’s LayerZero-powered cross-chain bridge.
Blockchain sleuth ZachXBT was first to flag the drain publicly on his Investigations Telegram channel around 2:52 PM ET. Within minutes, the rest of DeFi security accounts on X were piling on. From Cyvers and PeckShield to SlowMist, all confirming the worst. Security firm Cyvers revealed that the attacker had been pre-funded via Tornado Cash roughly 10 hours before the exploit, which is about as textbook as laundering prep gets.
By the time Kelp DAO posted its first public acknowledgment on X, the attacker had already moved on to the second stage of the heist.
What actually got hit
The target was Kelp’s Omnichain Fungible Token (OFT) adapter on Ethereum, the contract that holds the reserve rsETH backing every wrapped version of the token on 20+ Layer-2 chains. That list includes Arbitrum, Base, Blast, Linea, Mantle, Scroll, Mode, Swellchain, Zircuit, Berachain, zkSync, and others.
The way it’s supposed to work: a user burns wrapped rsETH on, say, Arbitrum. LayerZero delivers a cryptographically verified message to Ethereum. Kelp’s adapter sees the burn, checks it, and releases the same quantity of real rsETH from the reserve. One-to-one, clean, verifiable.
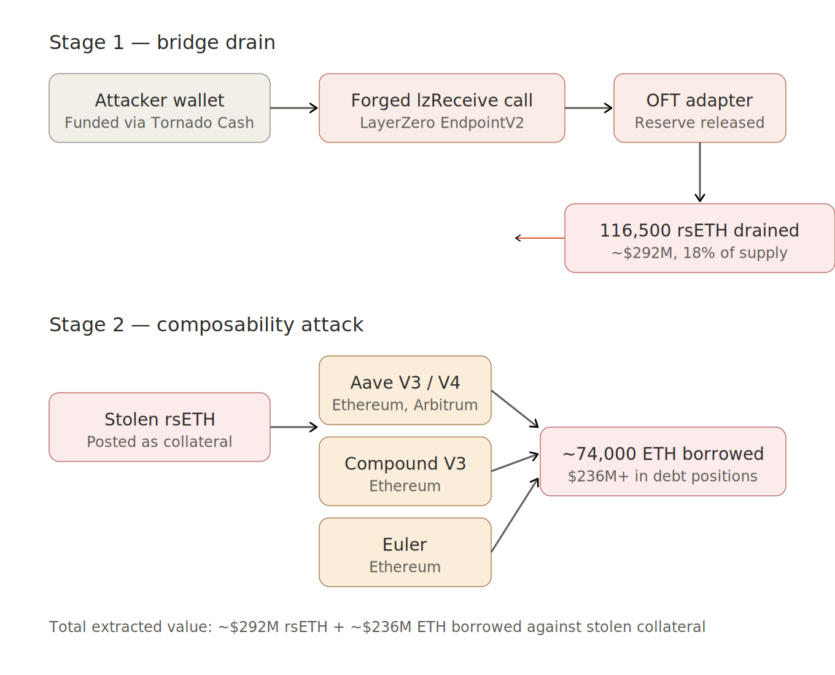
On Saturday, the verification step failed. The attacker “tricked LayerZero’s cross-chain messaging layer into believing a valid instruction had arrived from another network, which triggered Kelp’s bridge to release 116,500 rsETH to an attacker-controlled address.” One forged lzReceive call. No burn on the other side. No deposit. Just a packet that said “release the funds” — and the contract obliged.
What exactly broke? Kelp hasn’t said. The three plausible root causes are a DVN (Decentralized Verifier Network) misconfiguration accepting a forged packet, an OApp peer-mapping flaw trusting messages from an unauthorized source chain, or — worst case — an admin key compromise that let the attacker change the adapter’s config directly. Each one implies a very different fix, and until Kelp publishes an RCA, everyone else using LayerZero OFTs is operating on guesswork.
The second hack inside the first
Here’s what makes this one different from your standard bridge drain: the attacker didn’t just cash out and run.
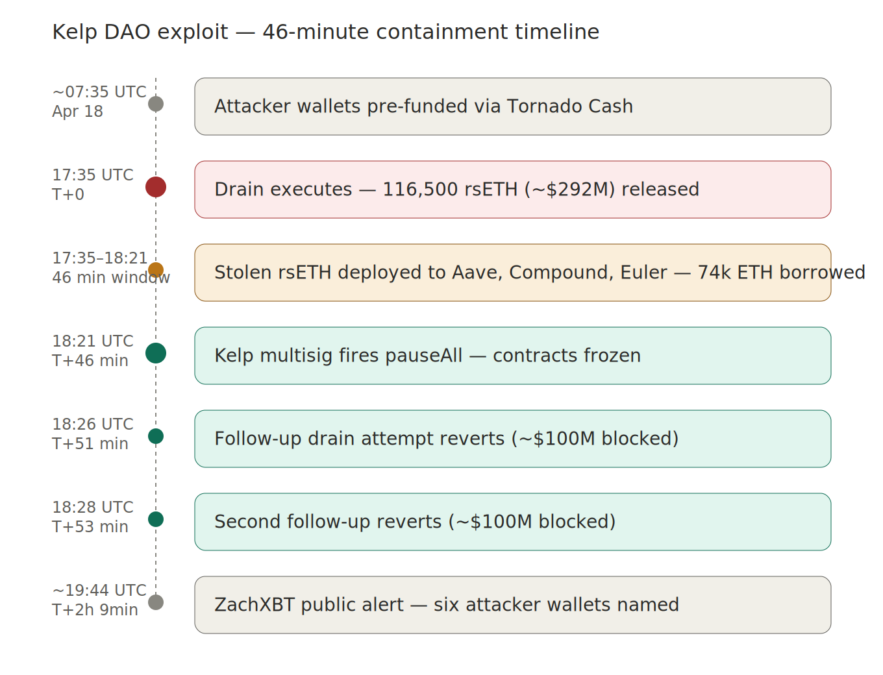
Within minutes of the drain, the stolen rsETH was deposited as collateral on Aave V3, Compound V3, and Euler across Ethereum and Arbitrum. Against that collateral, the attacker borrowed roughly 74,000 ETH and WETH building over $236 million in debt positions across three major lending markets. One wallet reportedly ended up sitting on about $120 million in borrowed ETH from Aave alone.
Solidity auditor 0xQuit, watching the positions build in real time, cut through the noise with a single tweet: “If you have WETH on Aave V3 Core, withdraw now.”
The trick here is sinister but simple. The attacker posted collateral whose redemption claim he himself had just stolen. The rsETH contract verifies normally. The price oracle quotes it at full value. To Aave, Compound, and Euler, it looks like legitimate collateral worth $292 million. Except the real rsETH backing it is already in the attacker’s wallet.
This is the mechanic that turns a bridge hack into cascading bad debt across DeFi. The $292M drain was just the entry ticket. The $236M+ borrow was the actual payout — because ETH is cleaner, more liquid, and not frozen behind a pause button.
What saved another $200M?
Kelp’s emergency pauser multisig finally triggered at 18:21 UTC — 46 minutes after the initial drain. The pause hit the LRT Deposit Pool, the Withdrawal Module, the LRTOracle, and the rsETH token contract itself. Everything froze.
And it’s a good thing it did. At 18:26 and 18:28 UTC, two follow-up transactions tried to drain another 40,000 rsETH each — roughly $100 million a pop. Both reverted. The pause held.
Without those 46 minutes of response time, total losses could have pushed near $391 million. The containment worked. The problem is that by the time the pause fired, the secondary attack on Aave, Compound, and Euler was already complete. You can’t unwind a loan that’s already been issued.
The contagion list is long
rsETH isn’t just a token. It’s a composable piece of DeFi infrastructure embedded in dozens of protocols. Once the exploit went public, the defensive freezes started rolling in fast.
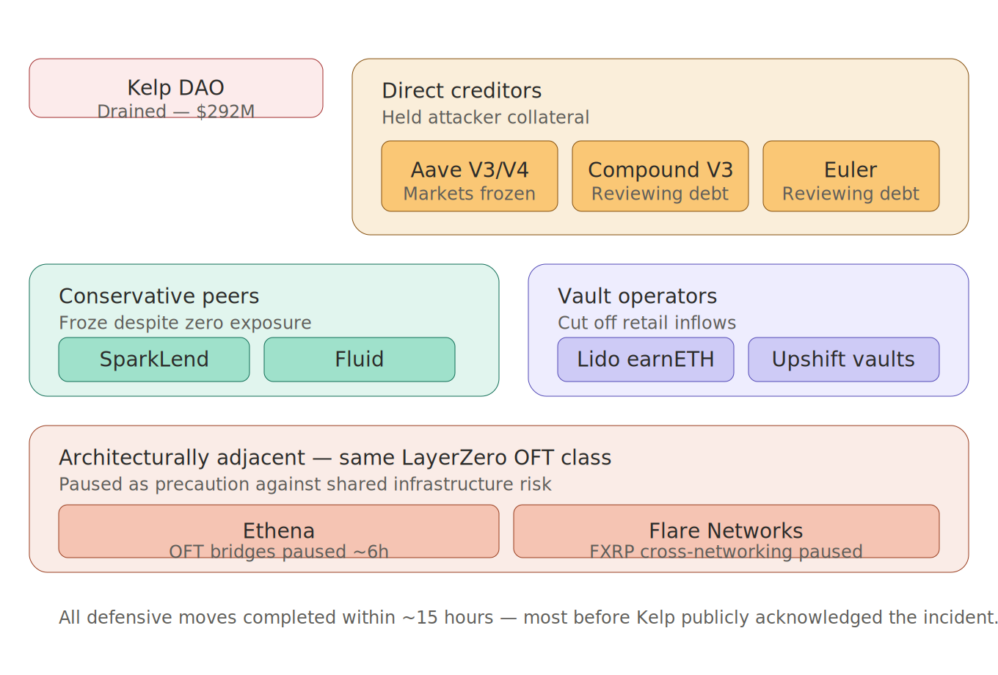
- Aave froze rsETH markets on V3 and V4. Founder Stani Kulechov posted on X that Aave’s own contracts were not compromised and that the freeze was precautionary.
- SparkLend and Fluid froze their rsETH markets. SparkLend reported zero actual exposure, crediting its conservative risk posture.
- Lido Finance paused deposits into its earnETH vault, which carries rsETH exposure — while stressing that stETH and wstETH are completely unaffected.
- Ethena temporarily shut down its own LayerZero bridges from Ethereum mainnet for roughly six hours, despite having no rsETH exposure.
- Flare Networks paused FXRP cross-networking via OFTs between Flare, Ethereum, Base, and other supported networks the following morning.
- Upshift paused its High Growth ETH and Kelp Gain vaults.
AAVE the token fell about 10–13% on the day as the market priced potential bad debt. ETH dipped around 3% in the same window. stETH and wstETH took mild sympathy hits around 4% before recovering.
Where’s the money now?
The six attacker wallets identified by ZachXBT sit across Ethereum and Arbitrum, holding a mix of rsETH, ETH, and WETH. As of April 19, none of it has moved to centralized exchanges. None of it has been pushed through Tornado Cash beyond the initial gas funding. No sanctions labels have been applied by OFAC or any other agency.
That’s unusual. Most exploiters in 2026 either move to mixers within hours or start testing CEX deposits to see what gets frozen. This one is just sitting. Which could mean a few things: the attacker is waiting out the initial attention, negotiating quietly, or — less charitably — figuring out which mixer still works after a year of aggressive OFAC designations.
What hasn’t happened yet is notable too. No white-hat bounty offer has been posted by Kelp as of this writing. No on-chain negotiation message to the attacker. No confirmed freezes at Binance, Coinbase, OKX, or Kraken. No public engagement with Chainalysis, TRM Labs, or law enforcement — or at least, nothing disclosed. The Euler ($197M, 2023), Poly Network ($611M, 2021), and KiloEx playbooks all involve some combination of those moves within 24–48 hours. Kelp is past that window and still quiet.
Kelp’s track record doesn’t help
This isn’t Kelp’s first rodeo. In July 2024, a GoDaddy domain-redirection attack hijacked the Kelp DAO frontend, draining multiple user wallets before the team caught it. Kelp pledged reimbursement and said it would move DNS providers. In April 2025, a fee-contract bug triggered a precautionary Aave freeze — no user losses that time, but it rattled confidence.
Saturday’s $292M drain is the third incident in under two years. The protocol has been audited by SigmaPrime, Code4rena, and MixBytes, and runs an Immunefi bug bounty capped at $250,000 (10% of funds at risk, with a $100K minimum for critical smart contract bugs). None of that stopped this one.
The pattern isn’t fatal plenty of blue-chip DeFi protocols have had multiple incidents and recovered — but it changes the recovery narrative. Kelp doesn’t get the benefit of the doubt this time. Users and integrators will want to see the full RCA, a concrete remediation plan, and ideally some form of compensation structure before trust rebuilds.
Where things stand right now
As of April 19, Kelp DAO’s contracts remain paused. No RCA has been published. No reimbursement plan has been announced. The attacker still holds the ~74,000 ETH. Aave, Compound, and Euler are still sitting with attacker-opened debt positions that they may or may not be able to cleanly liquidate.
The next 72 hours will tell us three things: whether rsETH’s peg survives when redemptions resume, whether the lending markets can absorb the bad debt without governance intervention, and whether anyone at Kelp can explain what actually broke.
This story is still developing. We’ll keep tracking the attacker wallets, any law enforcement updates, and whatever Kelp eventually puts in the RCA.
Also Read: Aave V4 Witnesses Accelerating Traction Just After Mainnet Launch