April 2026 was supposed to be a victory lap for crypto. Post-halving momentum, institutional inflows warming back up, and a DeFi sector that spent Q1 looking almost suspiciously quiet. Instead, the industry got hit with a reality check so brutal it’s already being filed next to February 2025’s Bybit disaster in the history books — except this time, the damage is worse.
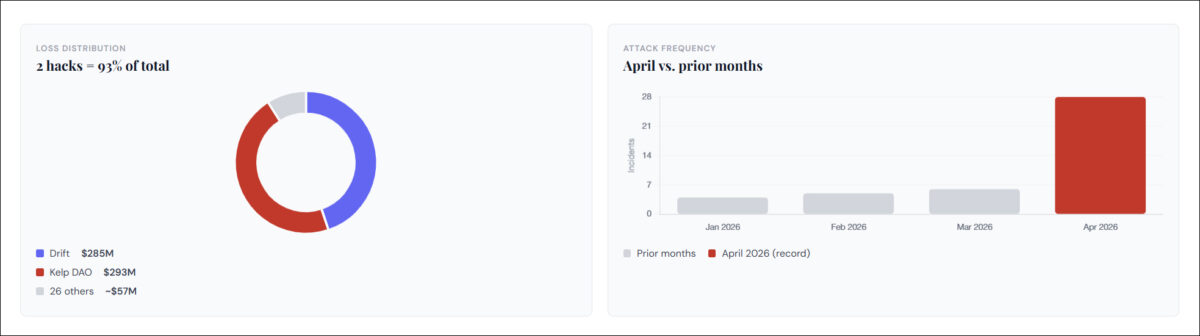
By the time April 30 closed, DeFiLlama confirmed attackers drained $635.24 million across 28 to 30 separate incidents — nearly one attack every single day since April 25. That’s 3.8 times the total losses from the entire first quarter of 2026 combined. Not a long, drawn-out bleed. A concentrated, relentless bloodbath that officially makes April 2026 the worst month for crypto security in recorded history.
April ends as the most-hacked month in crypto history, by number of incidents.
DeFiLlama, April 30, 2026
The Anatomy of a $635M Drain
The scariest part of April’s carnage isn’t the dollar figure. It’s the shift in how attackers are operating. The simple flash-loan exploits and smart contract logic bugs that dominated 2021–2024 are fading into the background. Today’s attackers are hitting something more foundational: cross-chain infrastructure, developer supply chains, and the human beings sitting behind admin keys.
Audits caught a lot of the obvious code flaws, smart contract bug incidents are reportedly down around 89% in some Q1 reports, but audits cannot stop a pre-signed nonce transaction, a forged LayerZero message, or a compromised deployer private key. That’s the gap attackers now live inside.
The Two Mega-Hacks That Defined the Month
TRM Labs confirmed North Korea-backed units were responsible for 75% of all crypto hack losses through April 2026, $577 million of a $759 million total, and have stolen over $6 billion in crypto since 2017.
What we are watching is not a North Korean campaign that is broader — it is one that is sharper. North Korea is moving faster and more precisely than ever.
Ari Redbord, Global Head of Policy, TRM Labs
Complete April 2026 Hack Timeline — All 28 Incidents
Every confirmed exploit across the full month of April, with filterable view. The 26 incidents outside the two mega-hacks alone totalled over $57 million in losses.
| # | Date | Protocol | Loss | Attack vector |
|---|---|---|---|---|
| 1 | Apr 1 | Drift Protocol | $285M | Social engineering, fake CVT token, durable nonce pre-signing |
| 2 | Apr 3 | Silo V2 | $392K | Misconfigured oracle |
| 3 | Apr 4 | TMM / BSC | $1.67M | Reserve manipulation |
| 4 | Apr 5 | Denaria Finance | $165K | Undisclosed |
| 5 | Apr 9 | Aethir | $423K | Access control on GPU bridge |
| 6 | Apr 12 | Hyperbridge | $2.5M | Fake state proof, Merkle Mountain Range forgery |
| 7 | Apr 12 | SubQuery Network | $60K | Access control |
| 8 | Apr 13 | Dango | $410K | “Donate negative amounts” logic flaw |
| 9 | Apr 13 | MONA | $61K | BurnAddress accounting bug |
| 10 | Apr 14 | Zerion Wallet | $100K | Hot wallet social engineering |
| 11 | Apr 16 | Rhea Finance | $18.4M | Flash loan oracle manipulation, 423 fake wallets, fake collateral on NEAR |
| 12 | Apr 16 | Grinex | $15M | Hot wallet compromise — 54 wallets drained (possible exit scam) |
| 13 | Apr 18 | Kelp DAO | $293M | LayerZero OFT bridge message forgery, single verifier compromised |
| 14 | Apr 20 | Juicebox V3 | $52K | Undisclosed |
| 15 | Apr 20 | Thetanuts Finance | $50K | Undisclosed |
| 16 | Apr 21 | Volo Protocol | $3.5M | Undisclosed |
| 17 | Apr 22 | Kipseli | $80K | Undisclosed |
| 18 | Apr 23 | Giddy Finance | $1.3M | Undisclosed |
| 19 | Apr 25 | Purrlend | $1.5M | Undisclosed |
| 20 | Apr 26 | Scallop | $150K | Undisclosed |
| 21 | Apr 27 | Singularity Finance | $413K | Undisclosed |
| 22 | Apr 27 | ZetaChain | $300K | Undisclosed |
| 23 | Apr 28 | JuDAO | $228K | Undisclosed |
| 24 | Apr 28 | Quant | $138K | Undisclosed |
| 25 | Apr 29 | Aftermath Perps | $1.14M | Undisclosed |
| 26 | Apr 29 | Sweat Foundation | $3.5M | Undisclosed |
| 27 | Apr 29 | Syndicate | $330K | Undisclosed |
| 28 | Apr 30 | Wasabi Protocol | $5M+ | Admin key compromise (wasabideployer.eth), UUPS proxy upgrade across 4 chains |
Wasabi Protocol — The Final Blow of April
On April 30, with hours left in the worst month in crypto history, Wasabi Protocol became its final chapter. The perpetual futures platform, ~$8.5M TVL across Ethereum, Base, Berachain, and Blast, was drained of over $5 million in approximately two hours. Not a smart contract bug. A key management failure — the same class of vulnerability that felled Drift Protocol 29 days earlier.
How the attack unfolded — step by step
Attacker obtained the private key to wasabideployer.eth — the single wallet holding ADMIN_ROLE across all PerpManager AccessManager contracts. No multisig. No timelock. One key, total protocol control across four chains.
Called grantRole() with zero delay, instantly elevating a malicious helper contract to admin status. A timelock would have given users 48+ hours to react. There was none.
Exploited UUPS (Universal Upgradeable Proxy Standard) to replace legitimate vault logic with malicious code. Called strategyDeposit() on 7–8 WasabiVault proxies with a fake strategy, triggering drain() — all collateral swept to attacker.
Upgraded WasabiLongPool contracts on Ethereum and Base to a malicious implementation that swept all remaining pool balances. Repeated across Berachain and Blast vaults.
Stolen assets (WETH, sUSDC, PEPE, MOG, NEIRO, ZYN, cbBTC, AERO, VIRTUAL) consolidated into ETH, distributed across addresses linked to Tornado Cash. Largest single outflow: 840.9 WETH (~$1.9M).
Action required for Wasabi users
If you have ever interacted with Wasabi Protocol, revoke all approvals immediately across Ethereum, Base, Berachain, and Blast using Revoke.cash, Etherscan's token approval checker, or Basescan. Do not sign any Wasabi-related transactions until the team confirms key rotation and full contract integrity.
April 2026 vs. Q1: How Bad Is the Gap?

| Metric | Q1 2026 (Jan–Mar) | Feb 2025 (Bybit) | April 2026 |
|---|---|---|---|
| Total stolen | ~$166.2M | ~$1.53B | $635M+ |
| Incidents | ~35 / 90 days | 1 event dominated | 28 / 30 days |
| Primary vector | Smart contract bugs | CEX hot wallet | Bridges + admin keys |
| Market impact | Largely contained | $5B+ market drop | $13B TVL wipeout |
| Attack pace | ~1 every 2.5 days | — | 1 every 1.07 days |
The Aave Contagion: $6.2B in Emergency Withdrawals
The Kelp DAO exploit deserves special attention for what it did to the broader DeFi ecosystem, not just Kelp’s users. Because rsETH was integrated as collateral in Aave, SparkLend, Fluid, and Upshift, the hack instantly created bad debt risk across all four platforms.
$8.4B in deposits left Aave within 48 hours as users scrambled to exit before anyone else did.
Aave’s token dropped 20% during Asian trading hours as the panic spread across time zones.
Aave founder publicly outlined a recovery plan acknowledging potential bad debt. Lido proposed donating 2,500 stETH to help offset the shortfall.
Spark Protocol attracted $1B in USDT deposits in a single week as capital rotated toward perceived safety.
$13B in total DeFi TVL evaporated in 48 hours — before most retail users had read a single headline.
This is what researchers call “shadow contagion”, one protocol’s failure quietly destabilizing several others that share exposure to the same asset. Kelp’s failure became Aave’s problem. Aave’s problem became Spark’s opportunity. $13 billion in TVL evaporated before most retail users even heard the news.
The Ripple Effects
The hacks didn’t just drain wallets — they triggered a $10 billion DeFi TVL wipeout in 24 hours (as of April 19). Every protocol felt the heat.
The replies poured in: some called it macro deleveraging, others pointed straight at the hacks, and a few saw it as “weak hands shaking out.” But the consensus was clear — the ecosystem is bleeding trust.
Then came this laser-focused post that went viral overnight:
The trust damage is harder to measure, but arguably worse. “Not your keys, not your coins” feels like a quaint slogan when audited, well-funded protocols are falling to human social engineering. Institutional players are responding the only way they know how: emergency rate limits from BitGo and Polygon, frozen bridge flows, and a lot of nervously worded risk updates sent to LPs.
The Pattern Connecting Every April Hack
Strip away the individual mechanics and one pattern becomes impossible to ignore: 95% of April’s losses came from infrastructure-layer attacks — not smart contract bugs. The attack surface has shifted permanently.
Wasabi, Drift, Grinex — one compromised key = protocol-wide event
Kelp DAO, Hyperbridge — forged messages, single-verifier configs
Drift (3 weeks of setup), CoW Swap domain hijack
Rhea Finance (423 fake wallets), Silo V2 misconfiguration
Aethir, SubQuery, Dango — broken permission models
CoW Swap — dApps are only as secure as their Web2 stack
What This Means Going Forward
Single EOA admin keys are indefensible in 2026. Both Wasabi and Drift prove one compromised key can trigger a protocol-wide drain in minutes. Multisig with genuine timelocks on all admin and upgrade functions is the baseline — not a premium feature.
Cross-chain bridges remain crypto’s most fragile point. Any protocol running bridge architecture without zero-trust verification and independent message validation is exposing every user on every chain it touches.
Audits alone are no longer sufficient. No code audit would have caught Drift’s social engineering, Kelp’s infrastructure compromise, or Wasabi’s key theft. The attack surface is now mostly human and organizational, not technical.
For users: revoke unused approvals (Revoke.cash), use hardware wallets, treat single-admin protocols as elevated risk, and follow on-chain security researchers for real-time threat intelligence.
A single point of failure anywhere in the chain that signs, deploys, or upgrades a DeFi protocol is no longer a defensible architecture in 2026.
Shalev Keren, Co-Founder & CPO, Sodot
Both records, most dollars and most incidents in a single month — broken simultaneously in April 2026 is not coincidence. It’s a signal. Without collective defense, April might not be the anomaly. It might be the preview.
The code is getting safer. The humans, and the bridges they trust, clearly are not.