Key Highlights
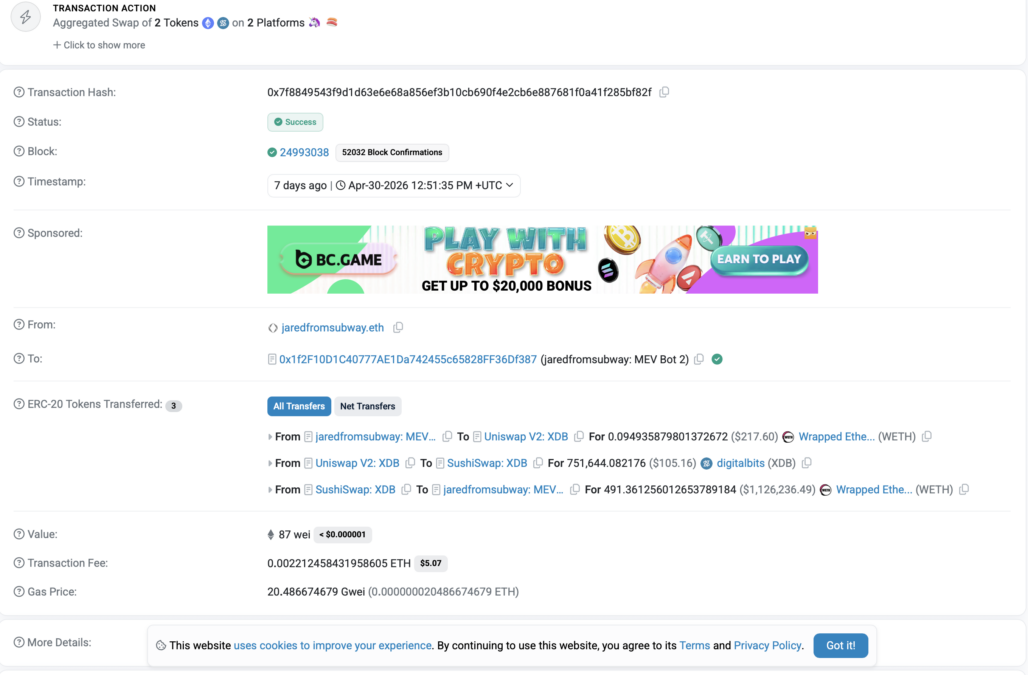
- Vitalik Buterin’s token swap was hit by a MEV sandwich attack, where a bot used his pending transaction to slightly worsen his trade price.
- The bot “JaredFromSubway.eth” used about $1.14 million in trading moves across exchanges to manipulate price before and after.
- This shows how MEV bots scan Ethereum’s mempool in real time and can still affect users, even key figures like Ethereum’s co-founder.
Ethereum co-founder Vitalik Buterin was reportedly affected by a Maximal Extractable Value (MEV) sandwich attack on April 30, according to blockchain data.
The incident occurred while Buterin was making a normal token swap on a decentralized exchange. An automated trading bot took advantage of the transaction while it was still waiting to be confirmed on the network.
How the attack occurred
Buterin was swapping 26,544 DigitalBits (XDB) tokens, worth about $3.86, for around 0.00197 ETH, worth about $4.56 at the time.
The trade was processed through Uniswap V2 routing, and his order was set with a very loose parameter that allowed the swap to go through regardless of price changes. This setting made his transaction easy to execute, but also made it open to manipulation by bots watching the network.
Bot activity around the trade
While the transaction was waiting in the mempool, a bot identified as “JaredFromSubway.eth” detected the pending order. The bot is known for monitoring Ethereum transactions and attempting to profit by altering market prices around them.
According to blockchain data, the bot first executed a large trade involving approximately $1.14 million in wrapped ETH across SushiSwap and Uniswap V2 liquidity pools, temporarily shifting the price of XDB before Buterin’s swap was processed.
After Buterin’s swap was completed, the bot placed another trade to reverse its position and lock in any small profit from the price change it created. This method of trading is called a “sandwich attack” because the victim’s transaction is placed between two trades by the bot.
In the end, Buterin received about 0.00197 ETH for his XDB tokens, and the loss from the price change was very small, only a few cents. The bot reportedly spent around $5.14 in gas fees, which are payments made to process transactions on Ethereum. In this case, the bot did not make a meaningful profit, but it still carried out the attack automatically.
How MEV works
MEV refers to the profit that can be made by reordering, inserting, or censoring transactions before a block is finalized. Sandwich attacks are one of the most common forms of MEV, where bots place trades before and after a target transaction to manipulate prices and extract value from the difference.
The bot “JaredFromSubway.eth” became popular during the 2023 meme coin trading boom. It often targeted high trading activity in coins like PEPE and WOJAK. At its peak, it was responsible for about 7% of Ethereum gas fees in one month and has reportedly made over $7 million from many small attacks across different trades.
Buterin has previously spoken about fixing MEV problems. He has supported ideas like encrypted mempools, which would hide pending transactions so bots cannot see them before they are confirmed.
Overall, this incident shows that even the creator of Ethereum can be affected by the same system issues he is trying to solve.
Also Read: Vitalik Buterin Targets Ethereum Bloat With “Restricted Storage” Idea