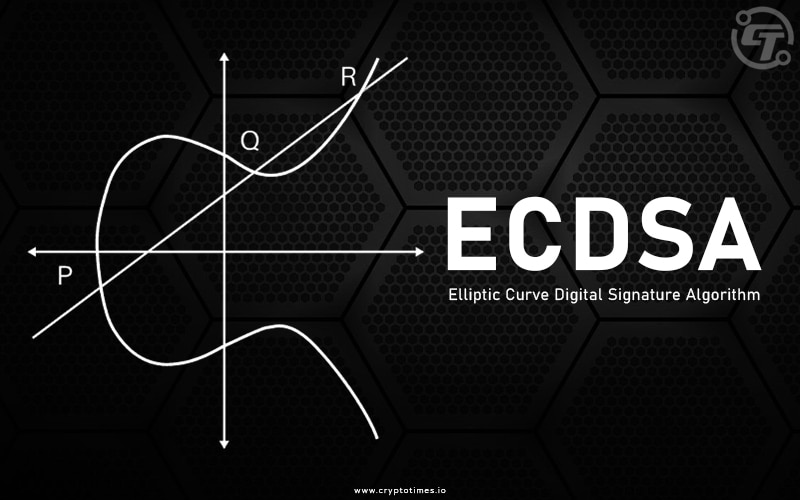
For most people, the inner workings of Bitcoin are complex and cryptic. What you need to know is that at its core, the magic of Bitcoin boils down to one key innovation – the Elliptic Curve Digital Signature Algorithm (ECDSA).
Simply put, this is a mathematical working of Bitcoin that allows Bitcoin wallets to transact with the network while remaining anonymous safely.
So, what proves that you own the Bitcoin you are spending without revealing your identity is the wonders of ECDSA.
Let’s ride together as we unlock the basics of this technology, its application, its security implications, and the future of ECDSA in Bitcoin.
Basics Of Elliptic Curve Cryptography (ECC)
Elliptic Curve Cryptography (ECC) is a form of public-key cryptography, that leverages the algebraic structure of elliptic curves over finite fields. This means it uses mathematical equations based on curved graphs to secure data. The strength of ECC lies in the difficulty of solving these equations, making it a robust choice for digital security.
In practice, a Bitcoin wallet uses ECC to generate a pair of keys: a private key, which is a randomly generated number, and a public key, derived from this private key using elliptic curve multiplication. The public key is your wallet address, shareable without compromising security.
Here is a Quick Look at How it Works:
An elliptic curve equation is selected, and a curve is generated from it on a graph. This curve has unique mathematical properties that make it hard to crack.
So a starting point on the elliptic is chosen somewhere on the curve. This is the private key, which is used to encrypt messages.
The public key is then generated from the private key and used to decrypt messages. These mathematical properties are what make elliptic curves secure.
Collins wants to receive 1 BTC from Grace. Grace then creates a Bitcoin wallet, which randomly generates a private key (point A) and the corresponding public address (point B).
So, when Collins shares his private address with Grace, Collin’s private key stays secret. However, when Grace BTC comes in, it is encrypted by Collin’s public key
Only Collin’s private key can decrypt and approve the transaction. Nobody is able to decipher his private key from her public address because of the ECC math.
Now that you have a good idea of what elliptic curve cryptography is about, let us have a look at the algorithms and how they work.
Elliptic Curve Digital Signature Algorithms (ECDSA)
ECDSA is a specific digital signature algorithm used in Bitcoin, that utilizes these ECC-generated key pairs. The private key must remain confidential, as it is used to digitally sign transactions, proving ownership of the funds without revealing the signer’s identity.
The ECDSA relies on elliptic curve cryptography to generate key pairs- one private key and one public key. Although the owner of the private key must keep it safe from other parties.
ECDSA has recently received significant attention from developers as an alternative to existing standard security systems. It also has different applications and uses within digital currencies, blockchain technology, and securing communication.
Application of ECDSA In Bitcoin
ECDSA (Elliptic Curve Digital Signature Algorithm), as said earlier, is the cryptography behind private and public keys used in Bitcoin. Interesting right?
Each Bitcoin wallet contains a public and private ECDSA key pair. The public key is the wallet address that can be openly shared to receive Bitcoin payments.
However, the private key must be kept secret, as it allows the owner to digitally sign and authorize transactions to spend bitcoins from that address.
When a user wants to transfer bitcoins to another party, their Bitcoin wallet will create a transaction message containing key details like the recipient’s address and amount to send. This transaction is digitally signed behind the scenes with the sender’s private key.
Once validated, the transaction is added to the blockchain ledger, and the transfer of the Bitcoin balance is completely secure.
The receiver can then only unlock and spend those bitcoins by presenting the private key corresponding to their receiving address in future transactions.
For crypto wallet owners, these keys must also be accessible when needed in order to unlock the funds. It is important to store the private key in a secure location, such as a hardware wallet, to ensure that it is kept safe from unauthorized access.
Security Implications
Aside from Bitcoin and blockchain, other technologies have adopted this security innovation. While there are a number of security advantages to the ECDSA, there are also some notable disadvantages. Here are some for you to look at:
- Security: ECDSA has a very high level of security, rendering it difficult to break the algorithm code. The algorithm has its foundation in elliptic curve mathematics, which is immune to cryptographic assaults and durable.
- Efficiency: The shorter signing keys produced by ECDSA can lower the speed of loading without affecting security, while also optimizing storage and reducing network congestion; quicker execution is also achieved.
Some possible security challenges include:
- Complexities: A solid grasp of ECDSA elliptic curve mathematics and protocol cryptography is required. ECDSA execution and implementation are challenging, and incorrect implementations might provide chances for hackers.
Some researchers warn that ECDSA may become vulnerable to quantum computing attacks in the future if quantum computers become highly advanced.
- Random key generation fails: Bitcoin’s ECDSA keys use 256-bit security, which is considered very strong encryption by classical computing but could potentially be broken if there is a random key generation failure.
Future of ECDSA In Bitcoin
The Elliptic Curve Digital Signature Algorithm has powered Bitcoin’s blockchain security since day one.
The cryptographic wizardry of ECDSA enables users to digitally sign transactions to prove ownership of funds in a way that preserves anonymity. Private keys remain hidden while transactions are validated publicly through mathematical signatures.
This breakthrough has allowed Bitcoin to become a decentralized global payment system without requiring real-world identities. ECDSA signatures enable trustless peer-to-peer transfer of value. Bitcoin’s creator, Satoshi Nakamoto, recognized that public key cryptography could unlock the holy grail of digital cash by solving the double spending problem.
Yet as integral as ECDSA has been to Bitcoin’s success, its long-term viability faces challenges. Quantum computing could someday possess the power to break elliptic curve encryption through Shor’s algorithm.
Although the threat timeline remains uncertain, ECDSA’s potential vulnerability to quantum brute forcing is taken seriously by cryptographers.
For now, ECDSA provides adequate protection, and replacing it is not urgently needed. But Bitcoin will likely implement quantum-resistant signatures at some point to stay ahead of threats.
Of course, any major foundational change would need extensive testing and consensus before deploying to the live network.
A good example of how the Elliptic Curve Digital Signature Algorithm (ECDSA) has been effectively used can be seen within the Altrix Edge bot, an advanced online trading platform.
Conclusion:
ECDSA signatures have ably secured Bitcoin transactions for over a decade now.
Therefore, understanding how this technology works not only provides insight into the inner workings of this technology and its wide adoption but also underscores its importance in the cryptocurrency financial system.
The essence of this technology is to ensure the integrity and authenticity of Bitcoin transactions. impossible to malicious attacks, and ensure efficiency, speed, and decentralized nature of Bitcoin as well as Blockchain.
But Bitcoin’s cryptography must keep evolving to remain resistant to emerging threats. While ECDSA still satisfies current security requirements, eventual migration to a successor quantum-safe scheme seems probable.