Beware of new scammers who are on the loose, ready to steal the money right under your nose without you even noticing it. The scam we are talking about is known as SIM swap fraud, which is a subtle attack that often goes unacknowledged until it is too late. These scams are so tricky that even prominent figures and entities fell prey to them and incurred a staggering loss of over $13 million.
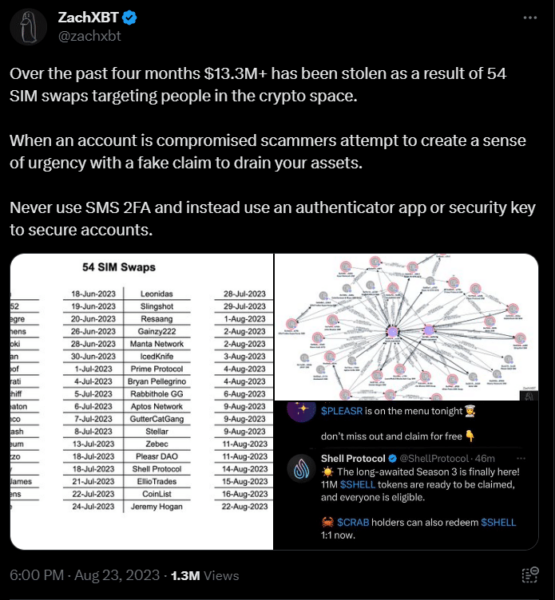
As per the startling revelations by renowned crypto detective ZachXBT, over $13.3 million was wiped from 54 victims’ accounts in just the last four months. The list of compromised accounts includes well-known crypto personalities such as OpenAI’s CTO, Mira Murati, the CEO of Bored Ape, Daniel Alegre, and the Aptos Foundation, among others.
So what is a SIM swap scam, and how do you prevent it? Tag along to save yourself from reeling in financial losses and find out what this insidious scam is all about.
What is the SIM swap attack?
Basically, cybercriminals deceive a mobile service provider into transferring a target’s phone number to a SIM card under their control. This manipulation grants the hacker access to all the accounts associated with the victim’s phone number.
The SIM card in your mobile device stores essential information, granting you the authorization to make calls and send text messages. Without a SIM card, your smartphone would only be suitable for tasks like browsing the internet via Wi-Fi or capturing photos.
After a successful SIM swap, the hacker gains unrestricted access to your SIM card, manipulating and taking control of all sensitive information and details on your phone.
The Phases of SIM Swap Attack
To understand this cyberattack in detail, here are the three phases of a SIM swap attack taking place:
The Initial Phase:
Essentially, a SIM swap scam occurs when criminals gain control of your phone by deceiving your mobile carrier into associating your phone number with a SIM card they possess. This allows fraudsters to hijack your mobile phone number.
The Intermediate Phase:
In order to carry out this theft, scammers first collect as much personal information about you as possible and then employ social engineering tactics.
Initially, the scammers contact your mobile carrier, posing as you and claiming to have lost or damaged their SIM card, which is actually yours. They then request that the customer service representative activate a new SIM card that the fraudster possesses.
This action transfers your phone number to the criminal’s device, which houses their own SIM card. Once your carrier executes this request, all phone calls and text messages that should be directed to you will be diverted to the scammer’s device.
The Theft:
Criminals can acquire control of your mobile phone number, enabling them to intercept your communications with financial institutions and other entities, specifically text messages. This allows them to receive any codes or password reset requests sent to your phone via calls or texts for all your accounts, granting them unauthorized access. This marks their successful infiltration.
On the Rise
The FBI has noted a rising trend in SIM swap scams, with a disconcerting upswing in reported cases. In 2021, the FBI recorded 1,611 instances of SIM swaps, resulting in losses exceeding $68 million.
This marks a significant surge compared to the period from January 2018 to December 2020, when the FBI received only 320 complaints related to SIM swaps and the victims incurred losses of approximately $12 million.
Ease of Scam: How Easy It Is to Defraud
The ease of this scam is part of why it is so widespread. SIM swap hacking can frequently occur using information that is publicly accessible or can be acquired through manipulative tactics.
Scammers can use your social media profiles to gather information on you that may help them impersonate you when they’re trying to pull off a SIM swap scam.
Other famous crypto scams, like smart contract exploits or exchange hacks, require high-level tech skills. This scam, however, has a relatively lower barrier of entry, and hence the low-effort, high-risk aspect of it contributes vastly to its surging incidents.
This digital thievery has permeated the crypto industry in its entirety, especially affecting the big names in crypto.
The Scam: Crypto Space
The most significant of these incidents pertained to Bart Stephens, the founder of Blockchain Capital, which had previously invested in early-stage companies like Coinbase, Kraken, and Worldcoin.
Stephens initiated a legal action against an unidentified hacker who, back in May, executed a SIM swap scam resulting in a loss of $6.3 million from his accounts.
Before the attack, an intruder gained access to Stephens’ account and sent him an email in which they boasted about their ability to remotely compromise any phone number within the contiguous United States, as reported by Forbes.
According to Stephens, the hacker breached his mobile account, placed an order for a new phone, and transferred his phone number to a SIM card inserted into the new device. Subsequently, the hacker leveraged his number to reset passwords and circumvent two-factor authentication measures.
Not only Stephens, but an alarming number of notable crypto personalities suffered losses including the CEO of Y Combinator, Garry Tan, the CEO of LayerZero, Barry Pellegrino, and even entities like CoinList and Pleasr DAO. A couple of months ago, British hacker Joseph O’Connor got a 5-year term for a SIM swap hack as a result of a theft of $794k performed on a crypto exchange executive in April 2019.
Signs You’ve Been Attacked
There are a few indications to diagnose your attack. Either they all start taking place together, or they do so gradually.
Here’s a list:
- You can’t make calls or send texts.
- You’ve been notified of activity elsewhere.
- You’re unable to access accounts.
- You find transactions you don’t remember making.
If you notice any of these signs together or individually, it is best to call your bank immediately.
How to Protect Yourself
Because SIM Swap has a low entry barrier, it becomes all the more important for users to be diligent about their cybersecurity.
Here are a few steps one can take to safeguard oneself against SIM swaps:
- ZachXBT opines that mobile carriers such as T-Mobile, Verizon, and AT&T must enhance their security measures. As recently as last week, Ethereum co-founder Vitalik Buterin’s Twitter account was hacked via a SIM swap attack. Fortunately, he has successfully regained control of his T-Mobile account.
- It is recommended that individuals use an authenticator app or a hardware wallet to secure their funds instead of relying on phone number authentication.
- To protect against SIM swap hacks, it is advised to avoid using SIM card-based methods for two-factor authentication (2FA) verification, like SMS. Instead, it is better to use authentication apps such as Google Authenticator or Authy, as suggested by Dyma Budorin, co-founder and CEO of blockchain security auditor Hacken.
- Additionally, the Chief Information Security Officer of SlowMist, 23pds, recommends implementing strategies like multifactor authentication and strengthening account verification by adding extra passwords.
- Users are also strongly encouraged to set strong PINs or passwords for their SIM cards or mobile phone accounts.
As the scope of crypto increases, so do the dangers and scams. It is essential to have a wide knowledge of all the latest frauds and a strong grasp of their diagnostics. Since high risk and high reward are true when it comes to crypto investing, let’s try to mitigate the risk wherever we can!






